Attacking Mobile Devices as a way into the organization
SMEs (Small, Medium and Enterprises) are beginning to see the risks that mobile devices are posing and there is a real void in that software space. Mobile Device Management is not mature enough to take on the challenge, Antivirus vendors are still toying with a solution that is effective and the move toward using Runtime Application Self-Protection (RASP), applications that use behaviours to help indicate and prevent compromise, are just beginning.
Experts agree that until we have a silver bullet that will not kill our battery life and will help protect us from Man in the Middle attacks, malicious applications or information leakage, our best line of defence is to educate ourselves. Mobile security is comprised mostly of individual responsibility. Follow some of these tips to be prepared when someone or something tries to compromise your device;
- Avoid unsecure Wi-Fi connections
- Keep Bluetooth out of discovery mode when not in use
- Use two-factor authentication whenever possible
You should also use basic security common sense, such as ignoring spam email, SMS messages and avoiding downloads that don’t come from an approved app marketplace (Apple’s App Store, Google Play, or a company-specific area).
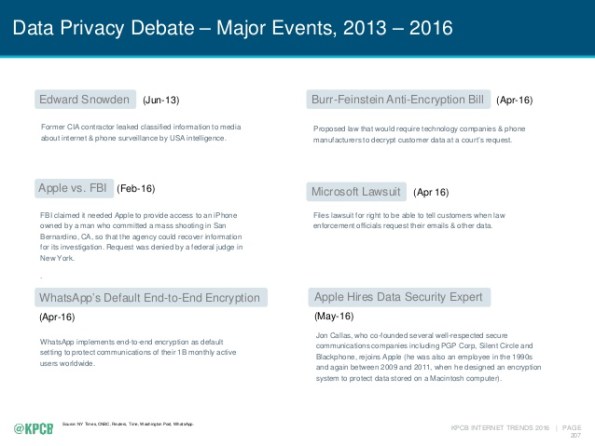
If you review the subject of security in the last few years you should find that more and more of the top privacy events are related to mobile.
We spend nearly half of our online time using mobile devices (http://www.comscore.com/Insights/Blog/Smartphone-Apps-Are-Now-50-of-All-US-Digital-Media-Time-Spent) using one type of application or another. The average device has at least 33 applications and nearly one quarter of them have at least one high risk security flaw (https://www.nowsecure.com/ebooks/2016-nowsecure-mobile-security-report/). The time to start analysing all of these applications for risk to the organization is now.