Forget SPAM, why not backdoor software instead
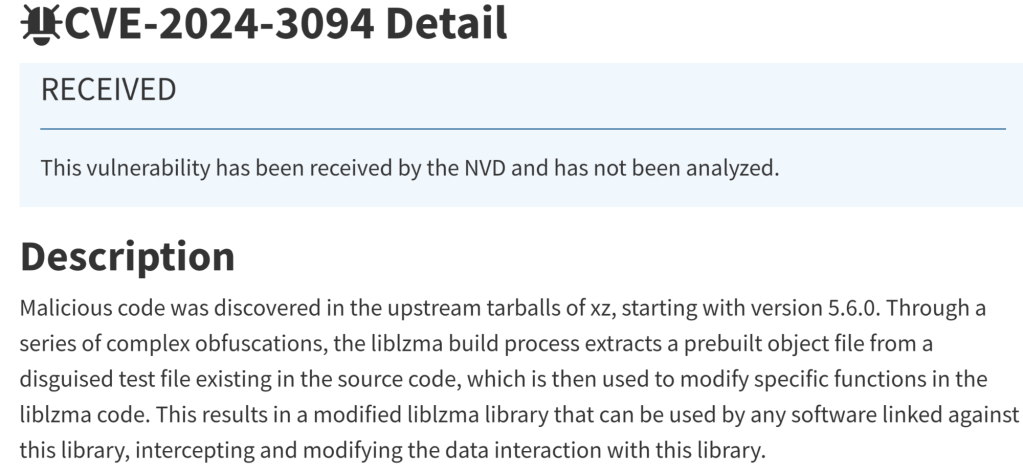
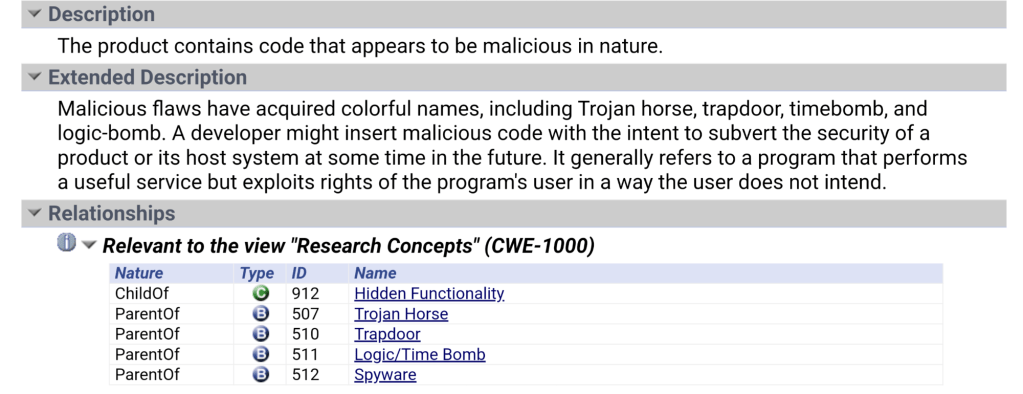
Open Source software is used by so many people, that it has become the target for a more sophisticated attacker. One that is so pernicious, it is known, in the Common Weakness and Exposure chart as CWE-506.
Let’s face it, over the last few decades, as the world was being eaten by software* we became too reliant on other people’s work. We ‘trusted’ what others were doing and relied too much on ‘good people doing great things’ so we could focus more on what we wanted.
The strength of open source (where so many eyes would review the code instead of just a handful of coders in a cave), makes us dependent on those same coders so if they don’t catch the malicious additions, who will?
Luckily, in such a short time, a few posts by a couple of curious sysadmins on Thursday, managed to catch this ‘feature’ being added to the source, which quickly produced this CVE (above) so patch your stuff before you too, become backdoored.
For my readers, I can only say that, if you use software in your business (that should be *all* of you), then you probably use open source so ‘Verify then Trust’ because this happens more often than you realize. Invest in your Security program which should include a threat analysis channel. We are at War with the hacker community and they only need one to win!
Want more info?
Pages
Archives
- September 2025
- July 2025
- November 2024
- July 2024
- June 2024
- April 2024
- March 2024
- December 2023
- September 2023
- July 2023
- June 2023
- August 2022
- July 2022
- June 2022
- May 2022
- April 2022
- February 2022
- January 2022
- July 2020
- June 2020
- May 2020
- April 2020
- March 2020
- February 2020
- December 2019
- November 2019
- October 2019
- September 2019
- August 2019
- July 2019
- May 2019
- March 2019
- February 2019
- December 2018
- October 2018
- September 2018
- August 2018
- July 2018
- April 2018
- February 2018
- December 2016
- November 2016
- October 2016
- April 2016
- February 2016
- December 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- March 2015
- February 2015
- January 2015
- May 2014
- November 2013
- September 2013
- June 2013
- April 2013
- January 2013
- October 2012
- September 2012
- April 2012
- March 2012
- February 2012
- January 2012
- September 2011
- August 2011
- July 2011
- June 2011